Blog
The State of Cybersecurity in the Healthcare Sector
In this post, we take a look at cybersecurity in the Healthcare sector, the growing risk of ransomware and data breaches in the sector, and the larger outcomes of the the Change Healthcare attack in February 2024.
Exploring Access Control, MFA and the Principle of Least Privilege
Strong access control mechanisms form a part of all cybersecurity frameworks and data privacy regulations today, and should be on any security team’s or CISO’s priority list. Read on to learn why.
CIS Benchmarks: Securing Your Operating System Configuration
In this post, we explore the CIS Benchmarks, and how you can use them to assess OS configuration settings, ensure your systems remain secure, and prevent configuration drift.
Five Essential Cybersecurity Controls for SMBs
A basic cybersecurity program focused on high-impact controls can protect you against the vast majority of cyberattacks. Learn about the five essential security control categories for SMBs included in the UK NCSC’s Cyber Essentials framework.
How do you choose a GRC tool? Ask these 9 questions
How do you choose a GRC tool? Look for solutions that integrate features for compliance, sensitive data discovery, and risk mitigation, so you can to do all three more effectively.
Cyber Threat Trends in 2024: Common Patterns Seen in Key Industry Reports
In this post, we collate key findings from some of the big cybersecurity reports published this year to zero in on the biggest cyber threats in 2024, and identify approaches to defense that worked. This is the first in a three-part series.
The CIS Guide to Defining Reasonable Cybersecurity
The guide provides practical and specific guidance to organizations seeking to develop a cybersecurity program that satisfies the general standard of reasonable cybersecurity
Governance, Risk and Compliance (GRC) for Cybersecurity Practitioners
What has propelled GRC to the forefront of present-day cyber and business strategies? An overview of GRC and next-gen GRC tools for cyber leaders.
Understanding Shadow IT: Risks, Detection and Best Practices
Shadow IT – the use of technology and cloud apps without the knowledge of the IT department – can be a major risk for organizations today. Learn how to detect and manage the risk.
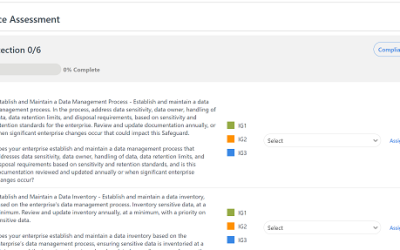
CYRISMA’s GRC and Compliance Assessment Module is Expanding!
The GRC Module and new compliance assessment features will allow you to track ALL controls included in the covered regulatory standards and best practice frameworks. Find compliance gaps, generate reports, run scans to get closer to compliance.