Data Discovery
Discover and classify what matters most - from endpoint to cloud
Gain full visibility into sensitive data across devices, servers, and cloud platforms - ensuring compliance and reducing risk with every scan.

Benefits

On-Prem & Cloud Classification
Discover and classify sensitive data across local systems and cloud services like Microsoft 365 and Google Workspace.

Automated Data Intelligence
Use custom regex or prebuilt templates to automatically tag and categorize data by type and regulatory scope (e.g., HIPAA, PII, PCI).

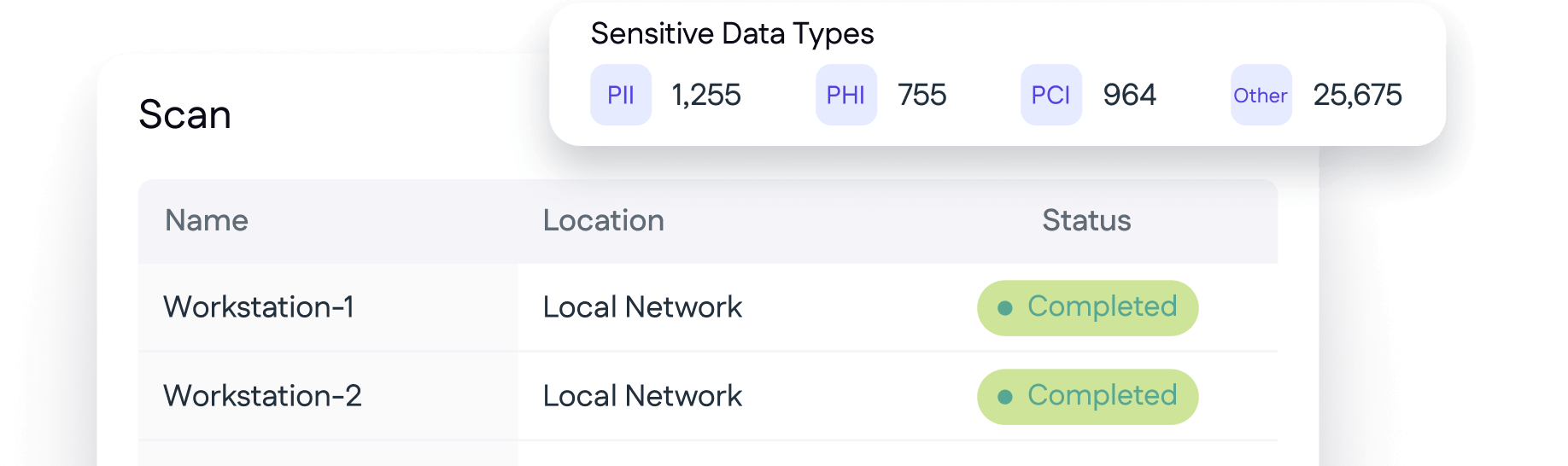
Actionable Risk Reduction
Identify overexposed files and take guided action - encrypt, move, or restrict access.
"Cyrisma has enhanced the capabilities that we offer to our clients from incident response to managed services. The product is very easy to install and setup with the ability to see results within minutes, Cyrisma is already showing a rapid ROI."
Features and Solutions
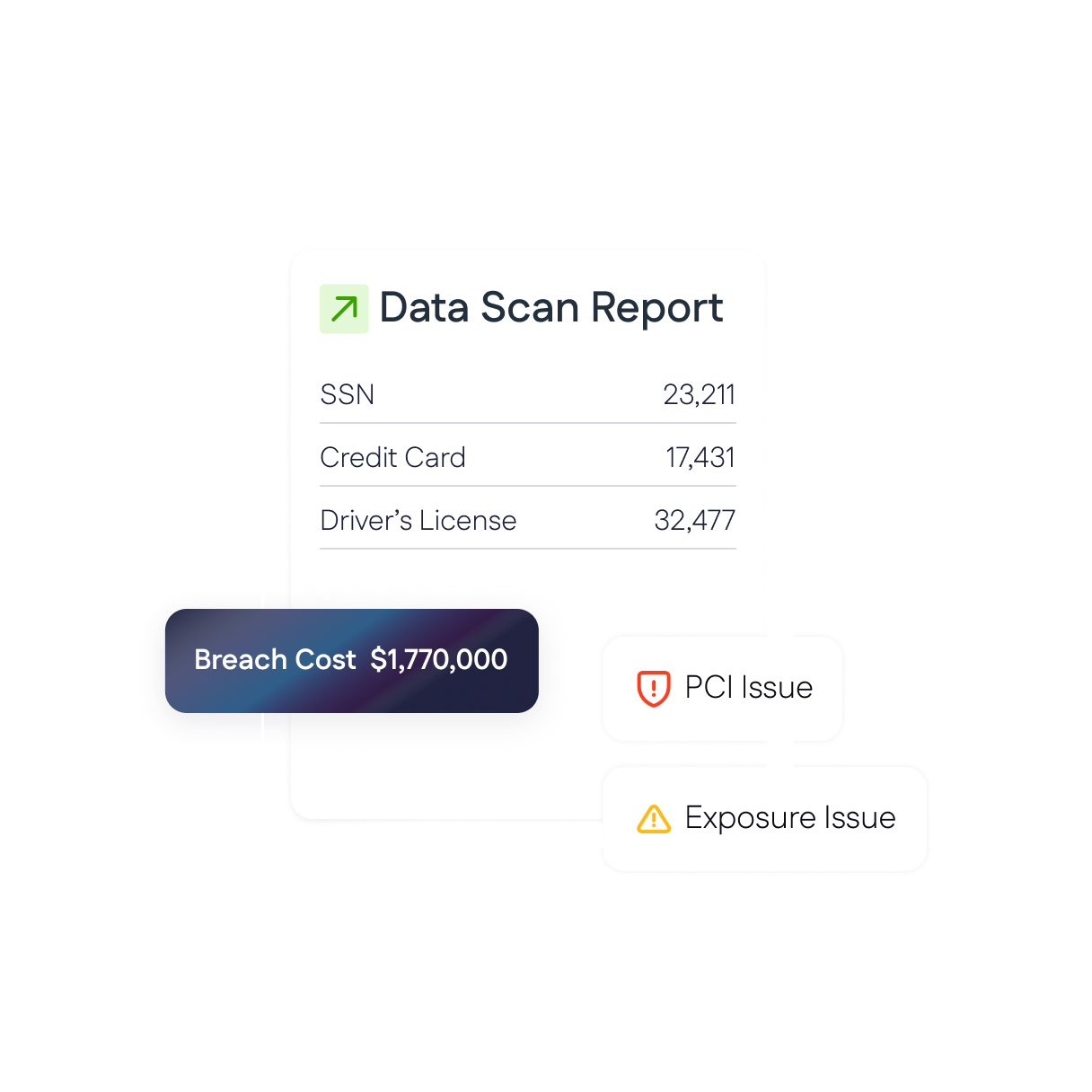
Discover sensitive data across local environments and cloud platforms like Microsoft 365 and Google Workspace using prebuilt templates to automatically detect sensitive data types.
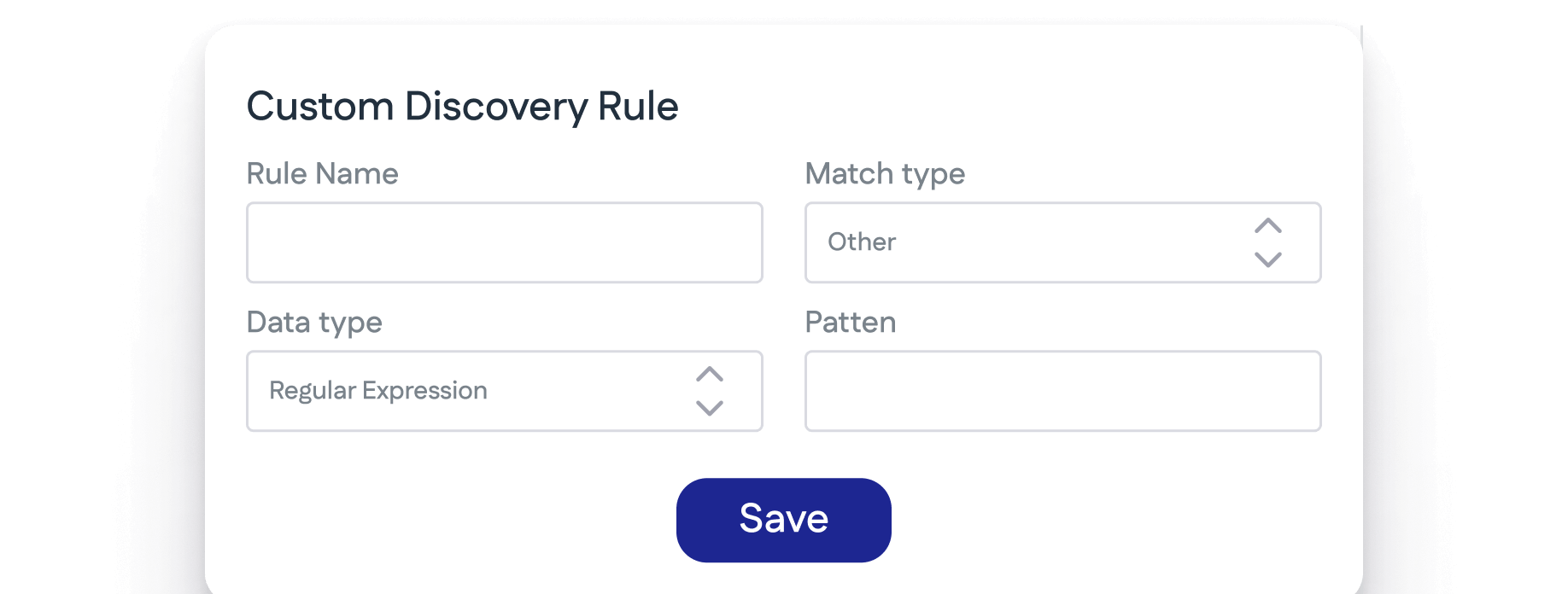
Build custom data discovery rules for customer-specific data types and needs.
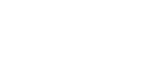
Generate detailed inventories to support audit and compliance requirements.

Sensitive Data Can’t Protect Itself
Data discovery locates and identifies sensitive or regulated data across your environment - an essential first step to secure data and comply with regulations.
We scan on-prem endpoints, servers, cloud storage, and cloud apps to uncover regulated data like PII, PCI, HIPAA, and more.
Yes - we support prebuilt templates (PII, PCI, GDPR), custom regex, and ML-driven pattern recognition to classify data automatically.
CYRISMA exports audit-ready reports, documents data inventory, and plots data locations - even linking findings to relevant frameworks like GDPR or CCPA.
Once identified, CYRISMA provides clear next steps - encrypt, restrict access, move, or delete - based on the data type and context.